AI-Assisted System Administration
January 2026: AI infrastructure added using Llama 3.3 70B Instruct on Mac Mini M4 Pro. The SysAdmin Agent Dashboard provides natural language system administration capabilities. Important: AI tools assist but do not replace cybersecurity expertise. See "AI Competency Paradox" in Risks.
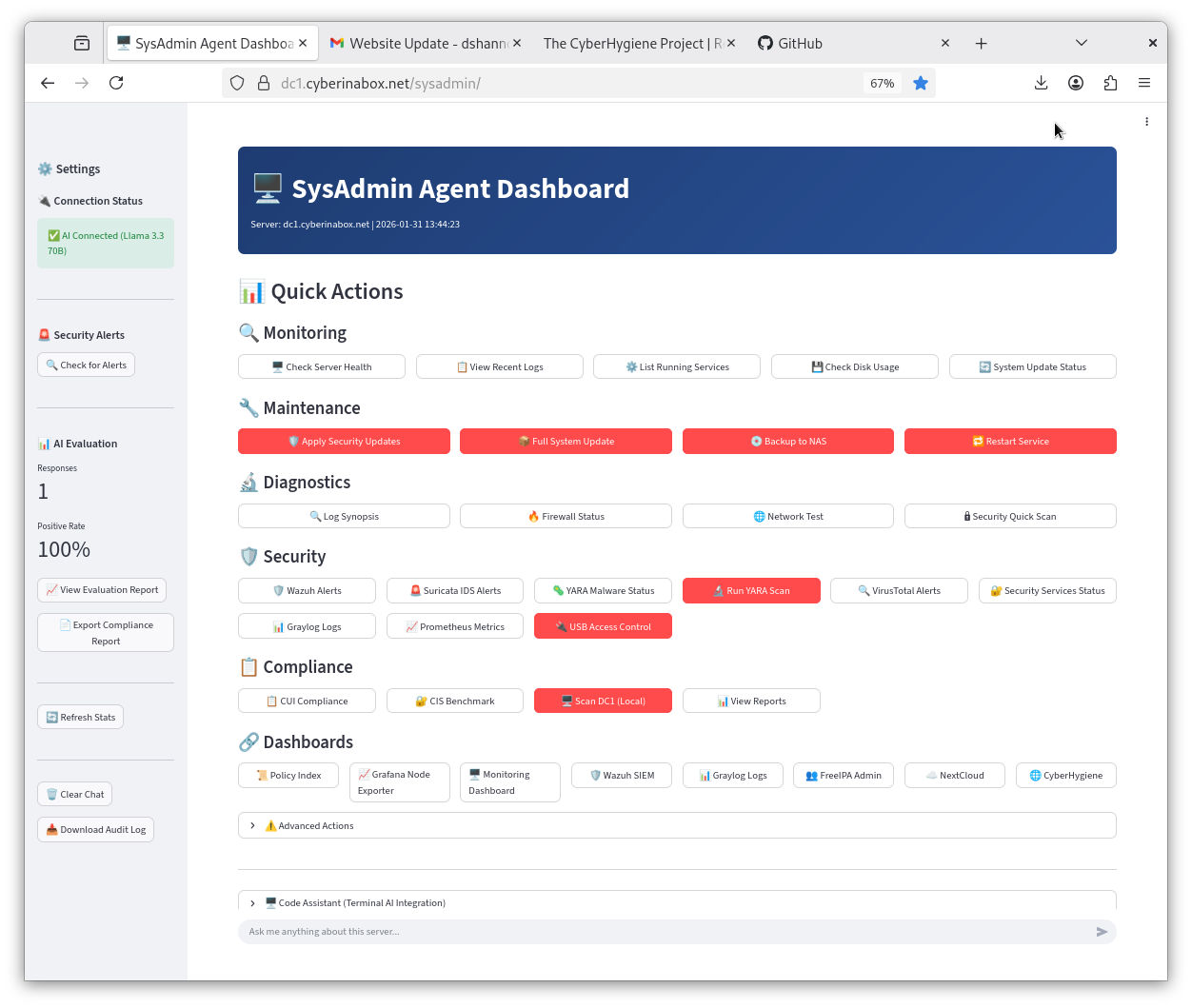
SysAdmin Agent Dashboard - AI assistance for system administration tasks
Implementation Details
- AI Model: Llama 3.3 70B Instruct (locally hosted)
- Hardware: Mac Mini M4 Pro, 64GB RAM
- Network: Internal only, TLS-encrypted (port 11443)
- Backend: Flask API with command whitelist
- Security: Human approval required for system changes
Capabilities & Limitations
- Can: Analyze logs, suggest troubleshooting steps, answer questions
- Can: Execute whitelisted read-only commands
- Cannot: Replace security expertise or judgment
- Cannot: Guarantee correct or secure recommendations
- Requires: Human review of all suggestions
AI Competency Paradox
AI tools can accelerate work for those who already understand what they're doing. For those who don't, AI can produce convincing-looking results that contain subtle errors or security gaps. AI assistance does not substitute for foundational cybersecurity knowledge. If you cannot evaluate whether an AI suggestion is correct, you should not implement it.
Why Local AI?
Running AI locally on the internal network provides:
- Data Control: Queries and responses stay within the environment
- No External Dependencies: Functions without internet connectivity
- Cost Structure: One-time hardware cost vs. ongoing API fees
Trade-offs: Local models may be less capable than cloud APIs; requires hardware investment; model updates require manual intervention.